LockBit and LockBit3 were the most deployed ransomware strains in the UK in 2022 and continue to present the highest ransomware threat to UK organisations.
LockBit and LockBit3, the improved version of LockBit, ransomware are constantly evolving, so attacks differ slightly from case to case. However, the structure and result of each attack are almost always the same.
LockBit and LockBit3 ransomware groups will first gain unauthorised access to your network or system through phishing emails, exploiting vulnerabilities, or using stolen credentials. As the attackers work their way through your system, they will start encrypting files so that they are inaccessible to you.
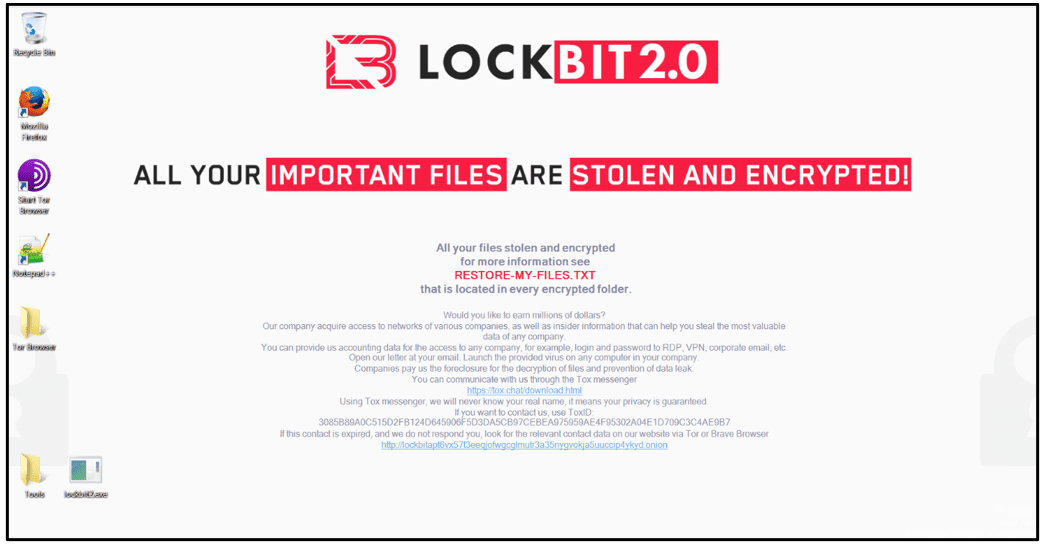
At this point, you will be presented with a ransom note on your system; this is usually in the form of a text file or pop-up message which will explain your files are encrypted and give details of how you will be able to get the decryption key.
LockBit and LockBit3 ransomware groups will usually request a ransom payment, most likely in cryptocurrency, in exchange for the decryption key. This will often come alongside a threat of leaking the data if the ransom is not paid within a certain timeframe.
Under attack from LockBit or LockBit3? Call us on 01202 308818 to get a response team at your site today.

Swift action is the best course of action. After receiving this message, you will need to get in touch with a ransomware recovery expert, such as Solace Cyber.
We know that a quick response is imperative in reducing the impact of the ransomware attack. We have two teams that allow us to provide national coverage, so no matter where you are, one of our teams can help. Arriving on-site the same day you make the call.
We will dispatch the closest team the same day you make the call, arriving on your site with all the necessary recovery equipment. As soon as we get to you, we will start work on understanding exactly what has happened, when it happened and where it happened. We will assess the situation, identifying vulnerabilities, attack vectors, data loss, and system impacts.
Once our team has a full picture of the attack, our on-site team and remote team will begin work to limit damage and prevent LockBit or LockBit3 from spreading.
Where possible, we will work to deliver a full restoration of the affected systems and services to normal operation, making backups where possible and repairing or replacing infrastructure that was compromised.
Once you are back up and running, we will complete a comprehensive report, going through the Digital Forensic Incident Report, which you will be able to use in any criminal prosecutions or insurance claims.

Solace Cyber are experts in dealing with high-stakes ransomware attacks from LockBit and LockBit3 ransomware groups.
Along with our expertise, there are many benefits of using our ransomware recovery service:
Experience - We have helped hundreds of businesses successfully recover from a ransomware attack - many from LockBit and LockBit3.
24/7 Security Operation Centre (SOC) Service - We manage our security operations centre all day, every day, so someone is around to deal with any situation at any time.
Accreditations - We are highly accredited as an approved partner of the National Cyber Security Centre (NCSC) and have several ISO accreditations.
Our approach - While we act fast in our recovery approach, we also implement a digital forensic analysis, meaning that we don’t overwrite the forensic data from LockBit or LockBit3 as we work. This means that you have evidence for criminal prosecution or insurance claims.
National coverage - We have teams in the North and South of the UK, enabling us to help you on-site no matter where you are.
Contact us now if you believe you are under attack from LockBit or LockBit3. We will act promptly and effectively to reduce your business downtime and the impact of the attack.
Call us on 01202 308818 or complete our form for a call back from one of our experts.
| Title | Available | Last visit | fqdn | Screenshots |
|---|---|---|---|---|
| LockBit BLOG | Yes | 2025-07-01 14:08:47.783694 | http://lockbit3753ekiocyo5epmpy6klmejchjtzddoekjlnt6mu3qh4de2id.onion | |
| Humanity check | Yes | 2025-07-02 10:16:32.722425 | http://lockbitqfj7mmhrfa7lznj47ogknqanskj7hyk2vistn2ju5ufrhbpyd.onion | |
| Humanity check | Yes | 2025-07-02 10:15:31.578667 | http://lockbitkwkmhfb2zr3ngduaa6sd6munslzkbtqhn5ifmwqml4sl7znad.onion |
Similar to legitimate software companies, they continuously develop and release new malware variants, with LockBit 3.0 being their latest ransomware iteration. LockBit's impact and tactics demonstrate their adaptability.
Total attacks
Victims by group
To gain access, LockBit exploits vulnerable Remote Desktop Protocol (RDP) servers or acquire compromised credentials from affiliates. They also use initial access vectors, such as phishing emails containing malicious attachments or links.
Once infiltrated, LockBit executes its ransomware through command-line arguments, scheduled tasks, and/or PowerShell scripts. The malware methodically collects credentials, disables security products, and skilfully evades defences. Before advancing to the final stage of file encryption, it meticulously clears logs, often operating discreetly for days or even weeks before the breach is detected.
Lockbit is a Russian backed ransomware group that first emerged in 2019 and has since become one of the fastest growing ransomware groups in the world.
An infection with LockBit, (or any ransomware) is characterised by your systems displaying a notice like the above with the perpetrator, a specialist cybercrime group, holding your infected systems and stolen data hostage until you pay a ransom. The ransom is typically demanded in cryptocurrency such as bitcoin.
Key Take Aways
If your systems display a message like below, they have been compromised by a LockBit attack.
You must not attempt to touch, restore or overwrite the data (explanation below).
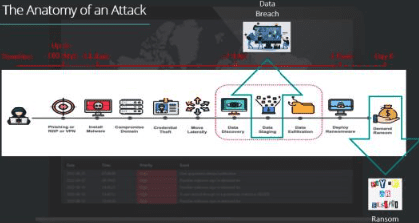
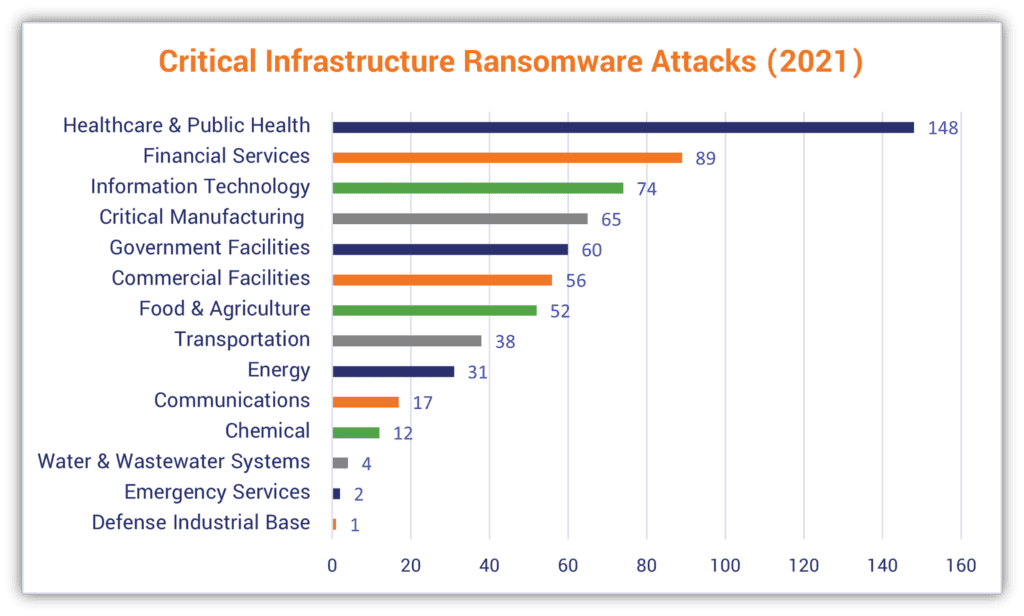
The likely chain of events is shown in the diagram above.
If you discover a physical break-in at your offices, your first thought would be to call the police; touch nothing and let them search for clues to the perpetrator. Then, work out how to get your business operations back up and running.
A cyber-attack requires the same logic. Your environment is a CRIME SCENE. It's imperative for the environment to remain untouched so that a forensic investigation can be carried out.
This is not a job for your IT team or MSP. There are digital forensic specialists available 24/7 who can assist you, just like in a physical crime.
Solace Cyber can offer a “Black Box” solution to allow you to get your business back in operation in a clean environment early in this process in parallel to the investigation and systems rebuild/restore.
Double extortion involves encrypting a victim's data making it inaccessible, and then exfiltrating sensitive information, such as personal or company data. The threat actors demand payment for both decrypting the files and preventing the release of the data on the dark web.
This dual threat significantly increases pressure on the victim to pay the ransom, even if they have backups, as the potential data exposure poses serious risks, including reputational damage and legal consequences. This tactic has become increasingly popular among cybercriminals because it maximises their chances of receiving payment.
LockBit first emerged in 2019 under the moniker ABCD Ransomware and is believed to have roots in Russia. It has since undergone several evolutions with Lockbit 3.0 being the latest variant. Lockbit 3.0 provides Ransomware as a service (RaaS) with the criminal group receiving payment from affiliates to launch cyber-attacks using their distinct brand of malware called “StealBit”. This malware automates the transfer of data to the intruder and is known for its rapid and efficient encryption capabilities. In 2022 they were the most deployed ransomware strain in the UK and continue to be the most prolific ransom group globally.
The LockBit group's modus operandi looks to leverage vulnerable Remote Desktop Protocol (RDP) servers and/or obtain compromised credentials from affiliates. They are known to employ common attack vectors such as phishing emails with harmful links, as a way of gaining initial access. In addition to this, they have been found to employ brute-force methods on weak RDP or VPN passwords and exploit vulnerabilities.
Once infiltrated, LockBit executes its ransomware through command-line arguments, scheduled tasks, and/or PowerShell scripts. The malware methodically collects credentials, disables security products, and skilfully evades defences. Before advancing to the final stage of file encryption, it meticulously clears logs, often operating discreetly for days or even weeks before the breach is detected.
LockBit is a type of Ransomware software that is currently threatening businesses in the UK, gathering money to fund terrorism around the world:
Useful Resources
“The first Cyber Security RANSOMWARE Incident was reported in 2019 and the growth since summer 2022 is significant, smaller organisations are being targeted”
“Cyber risks, such as IT outages, ransomware attacks or data breaches, rank as the most important risk globally (34% of responses) for the second year in succession – the first time this has occurred.”
Ref Allianz Risk Barometer 2023 - Rank 1: Cyber incidents
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
Similar to legitimate software companies, Lockbit continuously develops and releases new malware variants, with LockBit 3.0 being the latest ransomware iteration. LockBit's impact and tactics demonstrate their adaptability. To date, lockbit has amassed 1867 victims.
The chain of events that make up a typical ransomware attack is shown in the figure below. Depending on the incident, the response team may be involved at any stage in the attack, from reconnaissance through to post-encryption and random demand issuance.
When planning the response, it is important to determine what stage the attack is at, so that the attack can be better understood and short-term containment measures put in place to frustrate the attackers efforts to develop the attack any further.
Criminal organisations like Lockbit are paid by affiliates to launch cyber-attacks using their specific brand of malware that is known for its swift and efficient encryption capabilities. Even if the ransom is paid, the likelihood of having files decrypted and data restored is minimal, underscoring the necessity of employing a ransomware incident response team.
Check Links Monthly The NCSC have documented the deliberations for paying ransomware: https://www.ncsc.gov.uk/ransomware/home
Important Reminder: It is a criminal offense to pay money to people who are subject to financial sanctions. The list of who is subject to financial sanctions is constantly changing. The latest iteration can be found here: https://www.gov.uk/government/publications/financial-sanctions-consolidated-list-of-targets
Solace Cyber has consistently rescued customers without having to pay the ransom. This is our specialism. We can help.
However these systems continually evolve and LockBit has since attempted to resurface and announced on 26th Feb 2024 that is was back online.
Action Fraud is the UK national fraud and cyber crime reporting centre https://www.actionfraud.police.uk/ and is where you should report fraud if you have been scammed, defrauded or experienced cybercrime in England, Wales and Northern Ireland.
Solace Global was founded in 2010 as global experts in risk management and security, offering services such as Travel, Crisis, and Offshore Risk Management. With a 24/7 Security Operations Centre and an in-house intelligence team providing daily and weekly reports, Solace Global is accredited to ISO 27001, 14001, 45001, and 9001 standards. https://www.solaceglobal.com/
Solace Cyber was established in 2021, specialising in Cyber breaches, particularly Digital Forensics and Incident Response, Ransomware, Risk Management, and Information Security, along with Managed Security Services. The leadership team collectively possess over 20 years of experience in the IT and security industry. https://www.solaceglobal.com/cyber/
Solace Cyber is accredited to ISO 27001 and in 2022 gained the prestigious Cyber Incident Response (Level 2) accreditation with the National Cyber Security Centre in 2022. This accreditation represents the UK’s highest cyber security standards, providing top-tier incident response support and recovery.
Solace Cyber’s track record includes hundreds of successful response recoveries, providing Digital Forensic Incident Response services, 24x7x365.
A forensic analysis needs to be meticulous and a clean restore and recovery requires a wealth of experience not normally available in an in-house team who must provide a broader range of IT support skills:
Solace Cyber was established precisely for this scenario. We have a well-defined process for handling cyber-attacks like LockBit, which involves a 6-step approach:
It includes a thorough digital forensic analysis from step 2 where the output becomes a central component of business recovery. This is because understanding the attack is of critical importance:
It is critical that the analysis of digital evidence is carried out to an agreed plan. This will have been designed to provide the best and earliest chance of discovering a root cause, which is essential to inform remediation/eradication and recovery as well as supporting a legal take-down case if this is applicable. A legal take-down means we can assist in the legal enforcement that stops the criminals from publishing the data, thus undermining the ransom notice.
Solace’s Digital Forensic and Incident Response teams maintain consistent communication throughout. Dedicated Incident Managers and technical engineering leads provide updates during the Cyber Incident Response journey, utilising risk registers and working within change management processes, all from triage through to post-incident, delivering successful business recovery.
Most ransomware breaches cost approx £500K with smaller email data breaches in the realm of £50K. There is a dichotomy of preserving the environment for forensics or recovering it quickly for less business interruption. The cost increases the longer it takes to identify the breach and resolve it.
A Cyber Security insurance claim is complex and includes reasonable expenses to investigate and remediate an incident along with cover for legal, business interruption, criminal liability, employment liability and ransom policies. The insurance industry is liable to deliver the
business recovery BUT Cyber insurance is viewed as volatile within the industry and many insurance policies are not being validated correctly.
Navigating through this requires experience, which is where Solace Cyber can help.
Solace Cyber has been successful in more than 40% of our insurance claims. We can help.
Your servers may be out of action for between 2 weeks and 6 months. You will have a business continuity plan to help your continue with your business operation during this time. Consider the value of the data you no longer have access to, what you need now, and what you may want later.
Solace Cyber can offer a “Black Box” solution to allow you to get your business back in operation in a clean environment early in this process in parallel to the investigation and systems rebuild/restore.
It should be noted that decryption tools are usually available 6 months after the encryption is launched and it may be that some of the encrypted data can be recovered after this has been released.
Almost certainly, yes.
It is possible that some of the data lost is classified as “Personal Data” to your customer. You have a legal obligation to protect that data but it may have been lost. You may also need to advise the Information Commissioner's Office https://ico.org.uk/.
Your insurer/legal council will advise you on what to do and how to proceed with this.
Solace has experience working with insurers and lawyers and can help in this relationship at this stressful time.
The Lockbit ransomware entered your system by one of several ways:
We recommend you adopt policies to:
After recovering from LockBit, Solace Cyber recommends that you update your business continuity plan to account for lessons learnt during this attack & recovery.
Solace Cybers’ support continues beyond the recovery process. Once your business is back up and running, we work with you to transform your cyber security through a threat-informed approach utilising our 9-step approach Solace Global - Cyber 9 Step Process
If your systems are showing signs of a LockBit attack, REMAIN CALM.
YOU MUST NOT TOUCH THEM, RESTORE OR OVERWRITE THE DATA (explanation above).
Contact Solace Cyber on 01202 308818 or complete our form for a call back from one of our experts. We will act promptly to reduce your business downtime.
If you think you are under a ransomware attack, don’t hesitate to get in touch with us to start the recovery process.
Complete the form to request a complimentary consultation with our specialists and get a plan of action in place immediately.
If you need assistance right away, we would recommend calling us on 01202 308818.
Solace Cyber, part of Solace Global, helps companies across the UK recover from ransomware attacks and data breaches.
Solace Cyber Limited is registered in England & Wales no. 14028838
Solace Cyber
Suite 6, Branksome Park House,
Branksome Business Park,
Bourne Valley Road,
Poole, BH12 1ED
United Kingdom